So what about Deploying Portainer on a Canonical Charmed Kubernetes cluster? We have seen how to do this on MicroK8s that you can check on the link above but Charmed Kubernetes is an entirely different environment.
Canonical Charmed Kubernetes is demanding in terms of resources and is usually deployed on a Cloud provider like AWS, GCP or Azure. Oracle Cloud, Rackspace and CloudSigma can also be used to deploy Charmed Kubernetes. Local deployment is also possible but you have to make sure you have the right infrastructure to be able to do this.
Some pre-reqs for this tutorial:
- Access to a Linux machine via a ssh terminal, preferably Ubuntu on the latest version;
- You need the snap package management app installed on the machine you are going to use for your deployment;
- Access to a Cloud Service Provider like AWS, GCP or Azure. We will use Azure as the CSP for this tutorial so make sure you know what can be the equivalent interfaces/commands if you use a different provider.
Initial setup
During the initial setup you will learn how to install the tools are required to setup Charmed Kubernetes and deploy the cluster.
Install the required tools
- Run the commands below on your terminal:
snap install juju --classicsnap install kubectl --classicapt -y install nmap-> this optional and can be used to check the ports that are open on the public IP address of your node(s)
Setup Juju with your cloud provider
- Add the cloud provider credentials with juju:
juju add-credential azure- You will be prompted to give this credential a name. You can use azure for example:
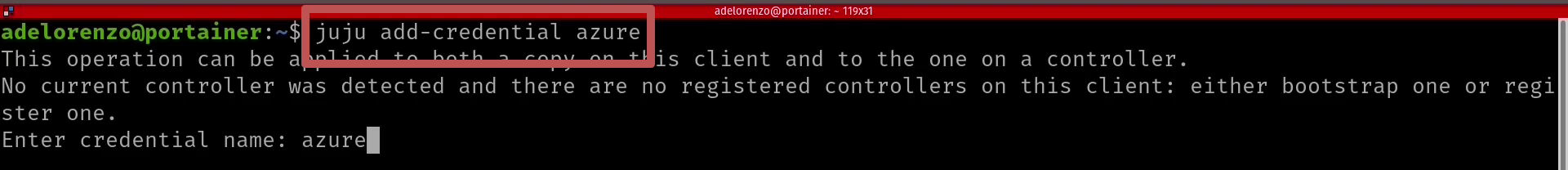
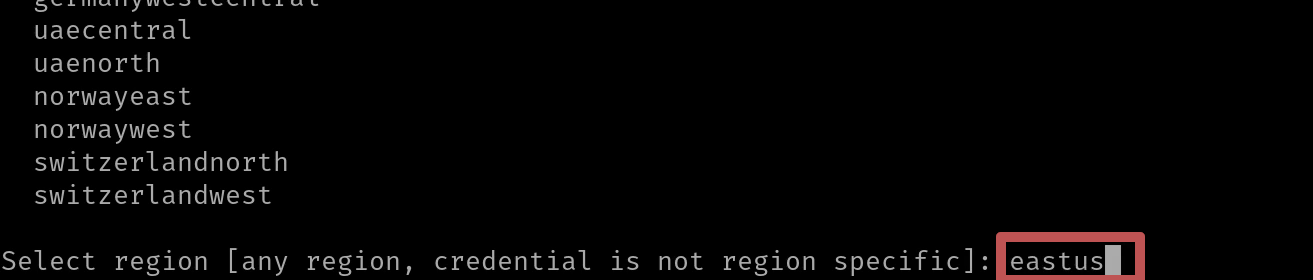
- The next prompt is the selection of the region you would like to use for the deployment. I picked eastus:
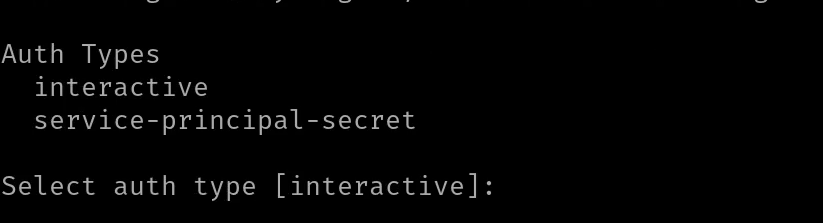
- The next step is to select the Auth Type, you can just go ahead and use [interactive] by simply hitting Enter:
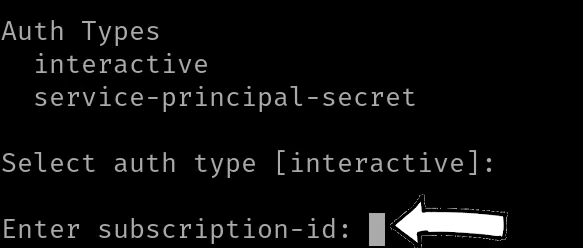
- The next step is to type the Azure Subscription ID that you want to use to deploy your Charmed Kubernetes cluster:
- A link to finish setting up the credentials will appear that you need to open in your browser and paste the code to authenticate. A unique code will be generated every time you add the credentials via juju:

- If all goes well the following message will appear on your browser window:
Deploying the Charmed Kubernetes cluster
- Start the bootstrap of the juju controller you will deploy on your cloud provider:
juju bootstrap azure <name>make sure to replace name with one of our preference. In this example I am going to use charmed01. This process can take up to 15 minutes: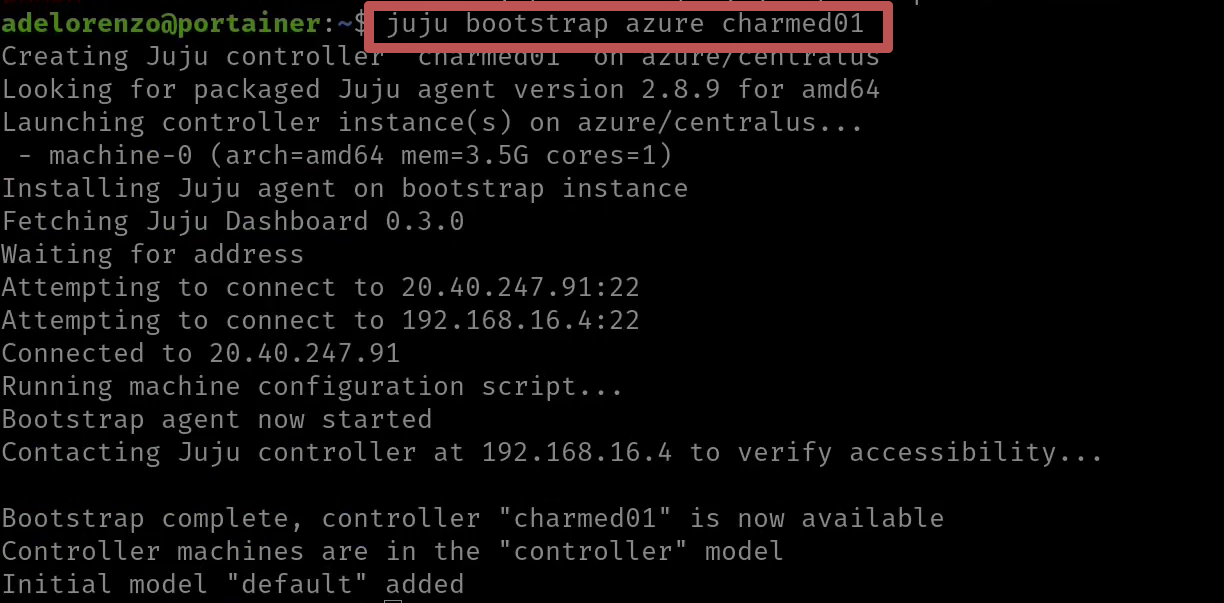
- Deploy your Charmed Kubernetes cluster:
- For a full cluster you can use
juju deploy charmed-kubernetes. This will deploy at least 8 machines with 2 redundant master nodes. - An alternative is to deploy a smaller cluster with one master + one worker node and add more nodes afterwards:
juju deploy cs:bundle/kubernetes-core-1200 - Add at least 2 more nodes with
juju add-unit kubernetes-worker -n 2. You can run this right after step #2 above.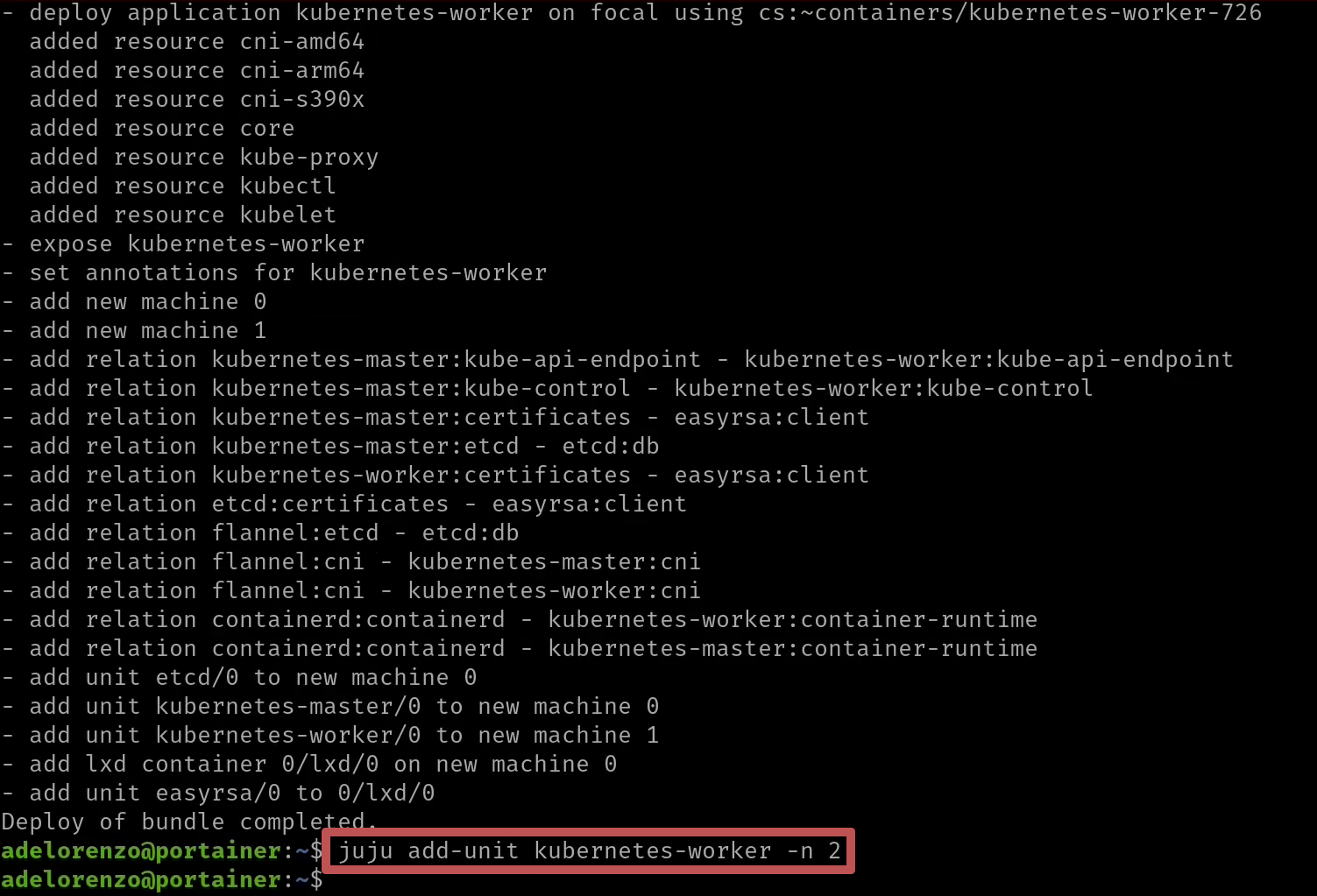
- For a full cluster you can use
- You can monitor the progress of the deployment of your cluster with
watch -c juju status --color: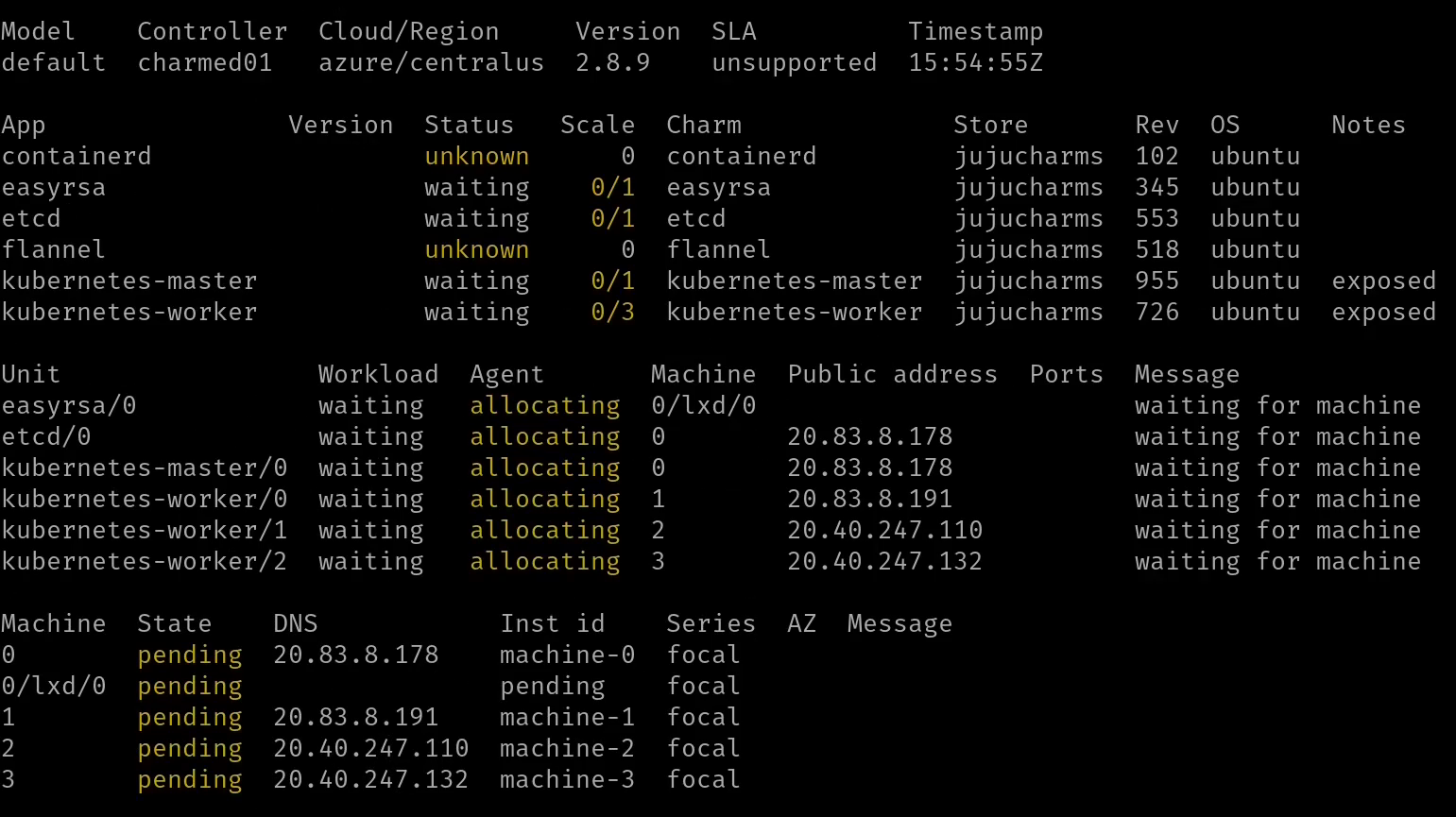
- This will take at least 20+ minutes. If all goes well you should see on your screen the following status:
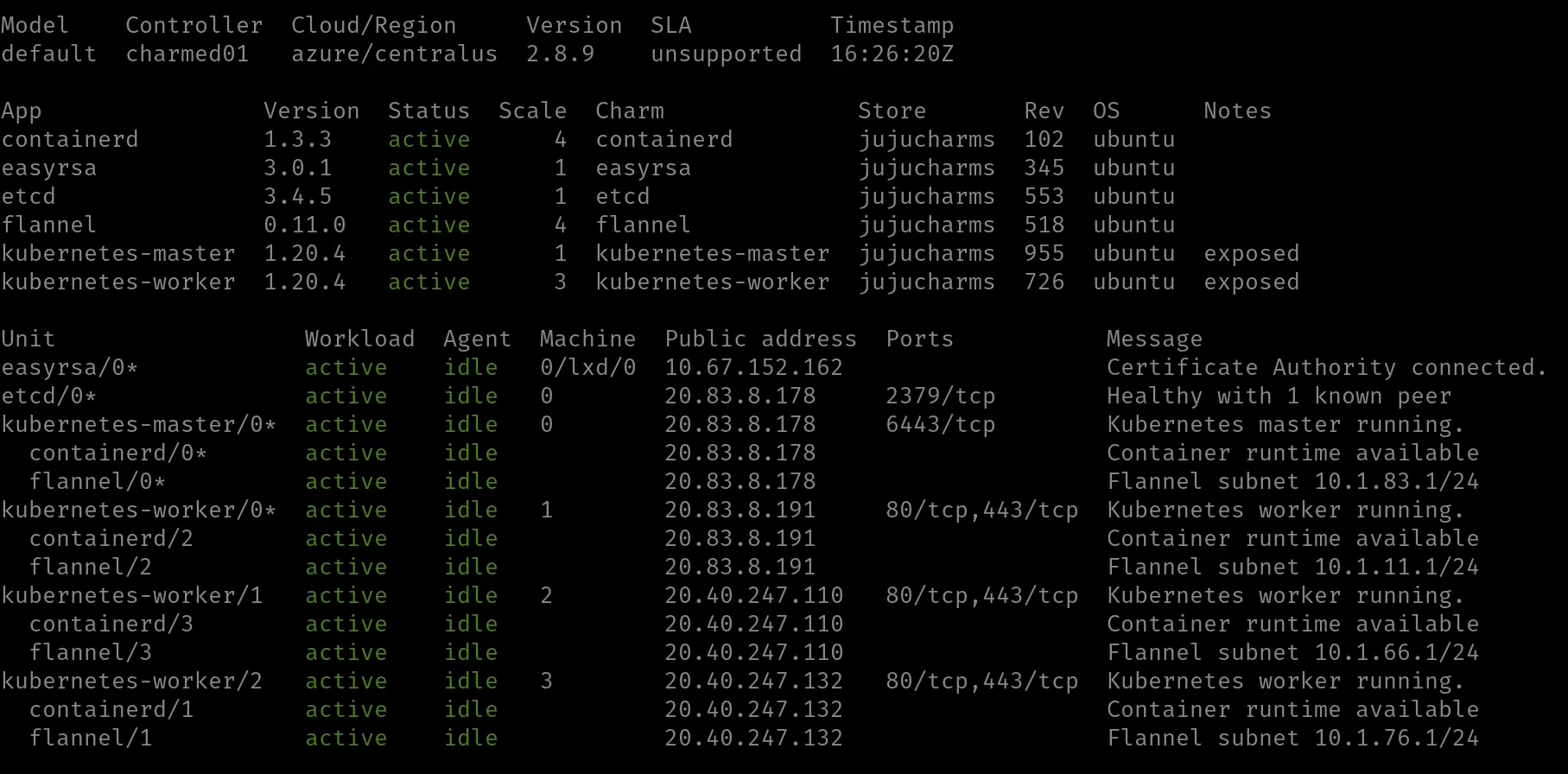
You can hit CTRL+C to exit the juju status screen and go back to the prompt on your terminal window. - Make sure you have a folder called .kube in your home folder. If you don't create is with
mkdir -p $HOME/.kube - Copy the config file from your master node in order to manage the cluster with kubectl:
juju scp kubernetes-master/0:config ~/.kube/config - Run a quick test to make sure you can access your cluster with kubectl with
kubectl get nodes. You should see your worker nodes on your cluster: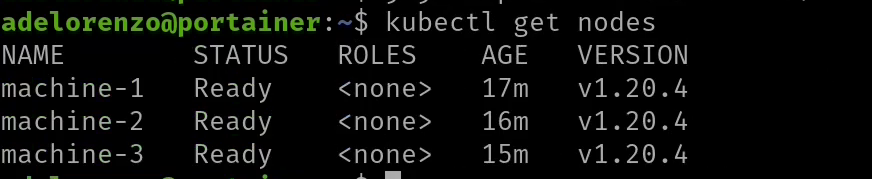
Deploying OpenEBS
- OpenEBS is a amazing storage option for Kubernetes. Please visit their website to learn more about this project.
- Start by enabling the iscsid service on all of your nodes with
juju ssh kubernetes-master/0 'sudo systemctl enable --now iscsid'. - Repeat this command for every worker node by replacing kubernetes-master/0 with kubernetes-worker/0 for example:
juju ssh kubernetes-worker/0 'sudo systemctl enable --now iscsid' - Enable running privileged services on your master node:
juju config kubernetes-master allow-privileged=true - Download the yaml file needed to deploy OpenEBS on your cluster:
wget https://openebs.github.io/charts/openebs-operator.yaml - Even though we enabled running privileged services on our master node we still need to make a small change to the privileged string on the file:
sed -i 's/privileged: true/privileged: false/g' openebs-operator.yaml && cat openebs-operator.yaml - Deploy OpenEBS with kubectl:
kubectl apply -f openebs-operator.yaml - You can check the status of the OpenEBS deployment with
kubectl get pod -n openebs - The deployment will finish once all the containers are running succesfully on your cluster:
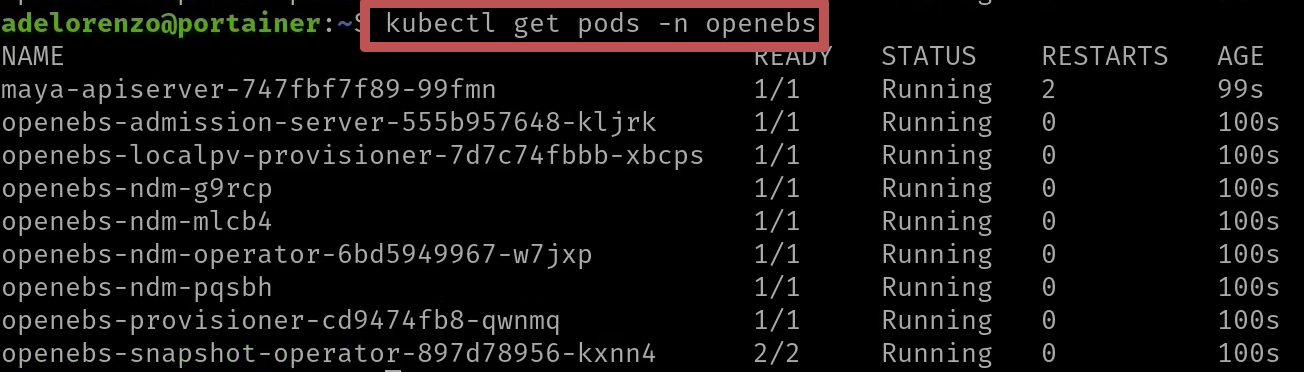
- Finally we need to ensure that the openebs-jiva-default storageclass is set as default by running:
kubectl patch storageclass openebs-jiva-default -p '{"metadata": {"annotations":{"storageclass.kubernetes.io/is-default-class":"true"}}}' - Run
kubectl get scto make sure the patch worked: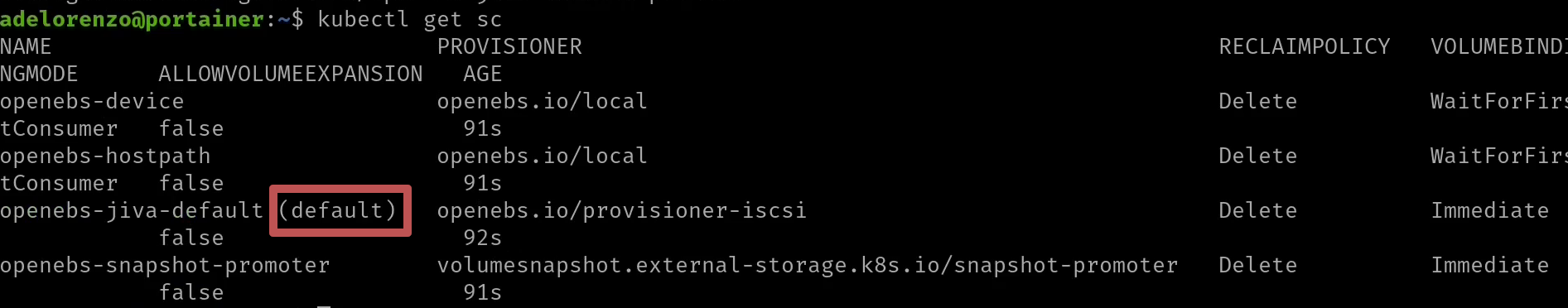
This is required otherwise Portainer cannot be installed
- Start by enabling the iscsid service on all of your nodes with
Deploying Portainer
- Installing Portainer is very easy. All you need is to run
kubectl apply -n portainer -f https://raw.githubusercontent.com/portainer/k8s/master/deploy/manifests/portainer/portainer.yamlto install Portainer using NodePort - You can check the status of the instalation with
kubectl get pod -n portainer. As soon as you see that the STATUS is Running then Portainer is ready to be used: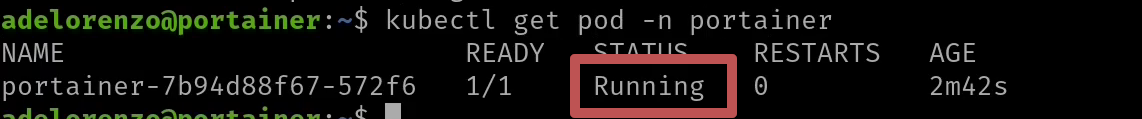
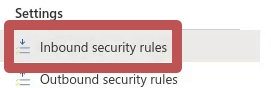
- Portainer when deployed on a NodePort will run on port 30777. We need to open this port on Azure (or on the CSP you deployed your cluster) to make sure it is accessible on the public IP of your node. You can do this by going to the All Resources page on your Azure portal and selecting the juju-internal-nsg in the juju-default-xxxxxxxx Resource group:

- Click on Inbound security rules:
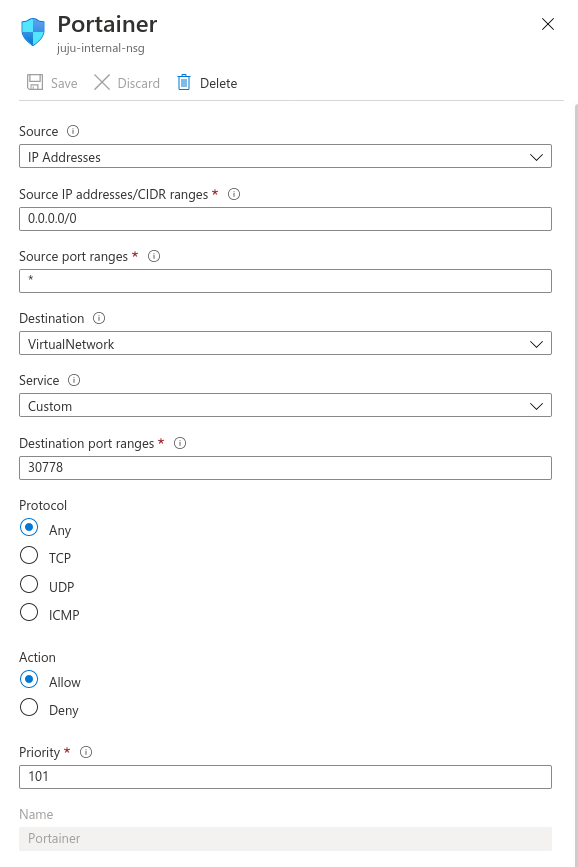
- Create a rule that will open port 30777 like this:
- You should be able to access Portainer by opening your browser with the public IP address of any of your nodes + port 30777. In my case the public IP of my master node was 20.83.8.178 therefore the link to open Portainer was http://20.83.8.178:30777:
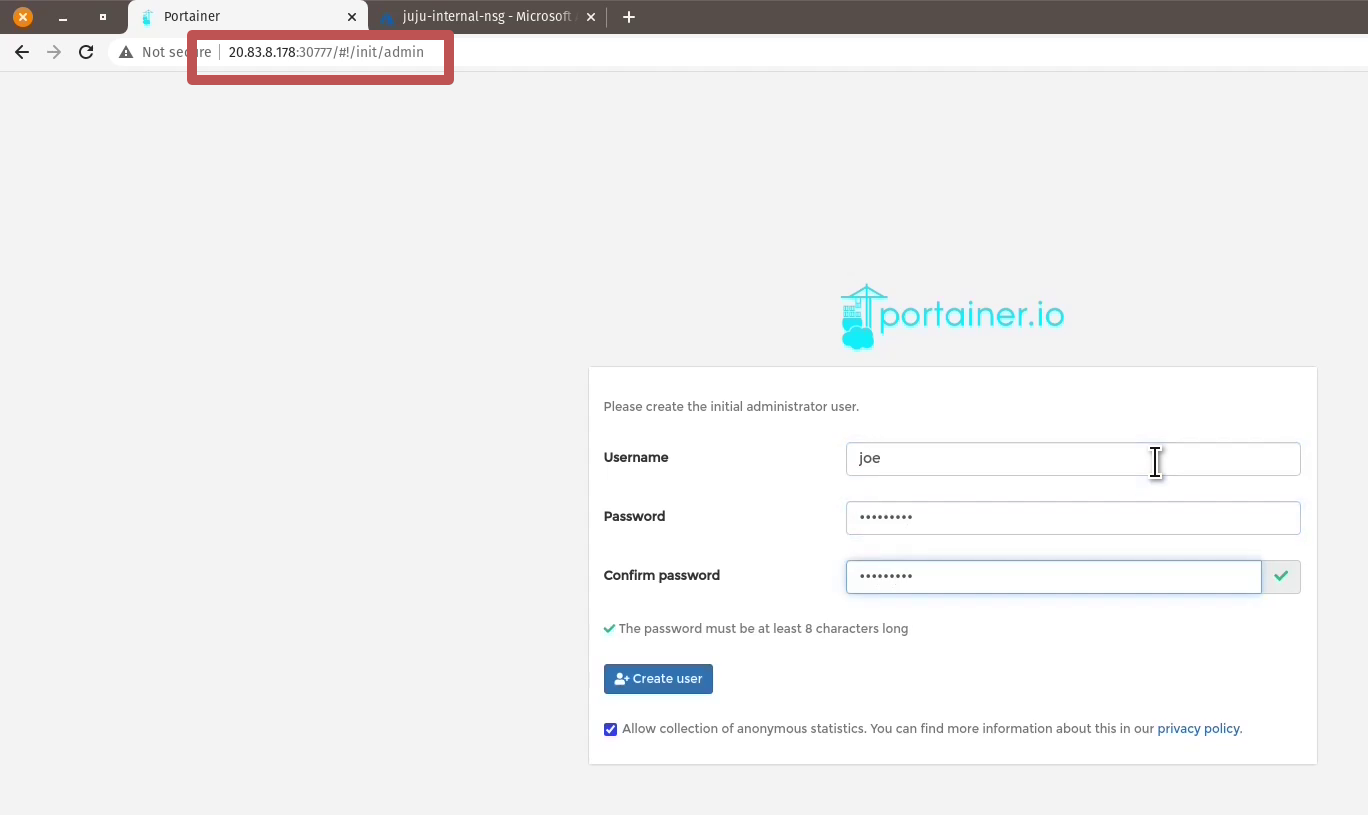
On this page you need to setup the administrator user for Portainer - The next step is to connect your Portainer instance to you Kubernetes cluster:
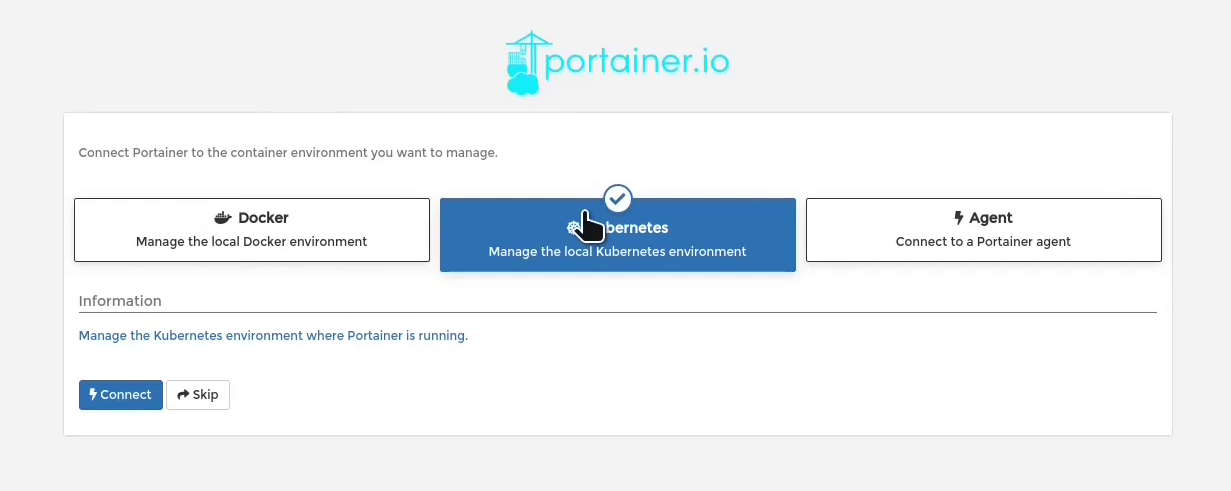
- The final step is to configure the Kubernetes features of your cluster on Portainer by enabling the metrics server features:

- and by enabling the openebs-jiva-default storage class with a RWO,RWX and Volume Expansion:
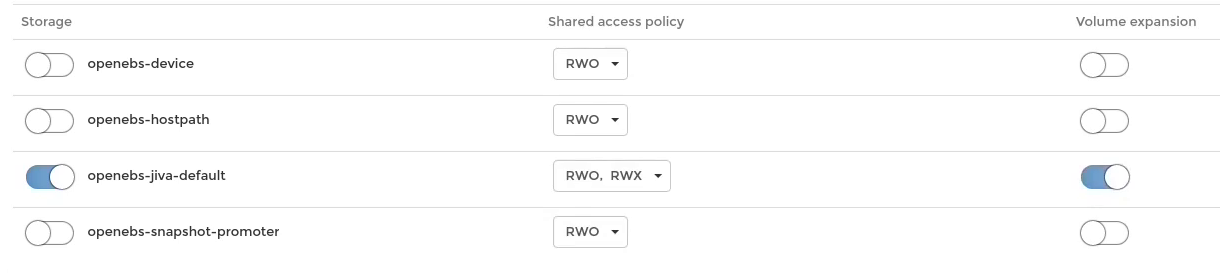
- Click on Save configuration and your Charmed Kubernetes cluster is ready to managed with Portainer!!
You can watch this all via youtube here:

COMMENTS