Enterprise-Grade Control & Compliance
Built for security, governance, and operational trust.




Centralized access & role management
Integrate with existing identity providers and enforce granular RBAC from one interface. Portainer centralizes authentication and authorization, removing the need for in-cluster frameworks and reducing attack surface.

Policy-Driven Security & Compliance
Enable OPA Gatekeeper, define change windows, set quotas, and stream audit logs to your SIEM - all directly within Portainer. Stay aligned with ITSM and regulatory requirements out of the box.

Lightweight, Self-Hosted Architecture
Enterprise control without the SaaS compromise. Run Portainer anywhere- on-prem, in cloud, or air-gapped - with a minimal footprint that keeps sensitive credentials behind your firewall.
Let our expert team help run your platform.
Kubernetes and Docker are powerful - but far from simple. With Portainer’s managed platform services, we’ll work alongside your team to set up and manage your container infrastructure, so you can move faster with less friction.
Accelerate adoption at Scale
Align teams, and deliver consistent, production-ready environments across every deployment.

Fleet-Wide Deployment & Management
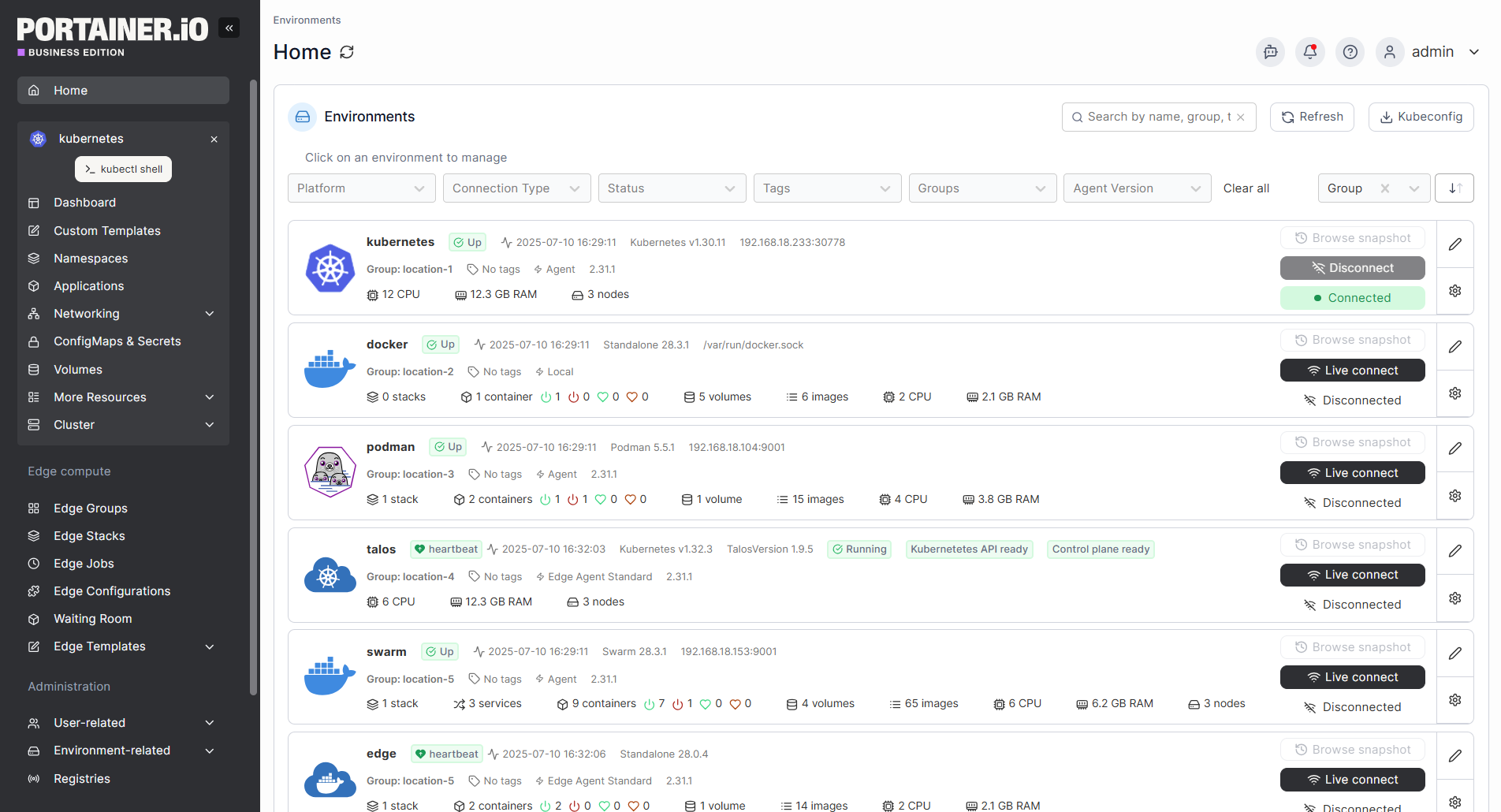
Manage thousands of clusters as easily as one. Deploy applications, enforce standards, and reconcile workloads across global fleets with full visibility and consistency.

GitOps Automation Engine
Automate with confidence, on your terms. Define administrator-controlled or self-service pipelines that reconcile automatically for secure, auditable, version-controlled operations.

Unified Operations & Observability
One dashboard for insight and action. Monitor cluster health, view logs, inspect YAML, and triage issues in real time with built-in alerting and enterprise-grade observability.



Foundational infrastructure for global enterprises
Seamlessly integrates across your stack
No need to rebuild your stack. Portainer works with the container platforms and environments you already trust - giving you centralized control and consistency across them all.
Your journey to accelerate operations
Contact SalesConnect with our team
Start with a conversation. Our experts help you assess your goals, existing infrastructure, and container readiness.
Audit your environment
We’ll identify opportunities to optimize operations and ensure your systems are ready for a unified control plane.
Deploy Portainer
Our team supports implementation, guiding you from setup to full-scale container management with confidence.


More tools.
Less guesswork.
Explore tools, training, and technical resources to help you deploy, manage, and grow your container environments with confidence.
Documentation
All the technical details, setup steps, and configurations you need – straight from the source.
Portainer Academy
Learn at your own pace with tutorials, walkthroughs, and guided training for every experience level.
Technical Architecture Overview
A deep dive into how Portainer works.
Portainer CE
The open source foundation of the platform. Try Portainer for yourself, experiment freely, and explore features.
.jpg)
.jpg)

















%201.png)






