Security and Compliance
- Cloud and Datacenter
- Industrial IoT and Edge
Portainer is a powerful policy and governance platform and an essential element to your container management stack, whether on the manufacturing floor or in the Public Cloud.
Secure, centralized access control
Orchestration platforms like Kubernetes are insecure by default, giving all users full access to the cluster. When you’re deploying at scale with a number of different classes of users needing access, this becomes a problem.
Portainer helps you to secure your environments and compute devices by giving you control over who can do what, keeping logs of what happens on the cluster, and providing backup and restore abilities for the Portainer database.
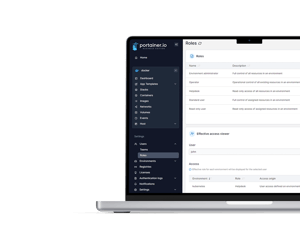
With our RBAC functionality, specify exactly what role each user or team has on each individual environment.
Configure access from the individual cluster up to your entire fleet or anything in between, quickly and easily.
Use our kubectl integration or proxy through Portainer with your existing tools, but with only the access level a user needs.
Avoid having yet another authentication system to manage by integrating with your existing LDAP, AD or OAuth provider.
Keep track of what actions are performed on your environments by your users in Portainer’s authentication and activity logs.
With our Open Policy Agent support, define under exactly what conditions your workloads are allowed to run.
Here's a scenario:
With Portainer, you can manage all of your environments, whether they be bare metal deployments or through a cloud provider, through the one interface. You can configure Portainer to use your existing authentication provider (for example, Azure Active Directory through Office 365 or OAuth through Google, as well as many other options) to provide a consistent, managed source of access credentials.
From there, you can set up each user and group with the required access levels on each cluster - for example, giving your junior developers access to create and edit workloads on your development infrastructure but no or read only access to production clusters. The users will only be able to perform the actions their role would permit them to, with actions taken logged in Portainer’s activity logs.
If a user needs to use a third-party tool to perform an action on a cluster, they can do that too through Portainer. With kubectl built into the Portainer UI as well as the ability for a user to download a kubeconfig file to use with other tools, users can still work with what they need but with the added security of their role restrictions protecting against unauthorized activity.
Secure access to your environments
Talk to our team about how we can help you set up secure environment access and meet your compliancy needs.