What can I do with Portainer?
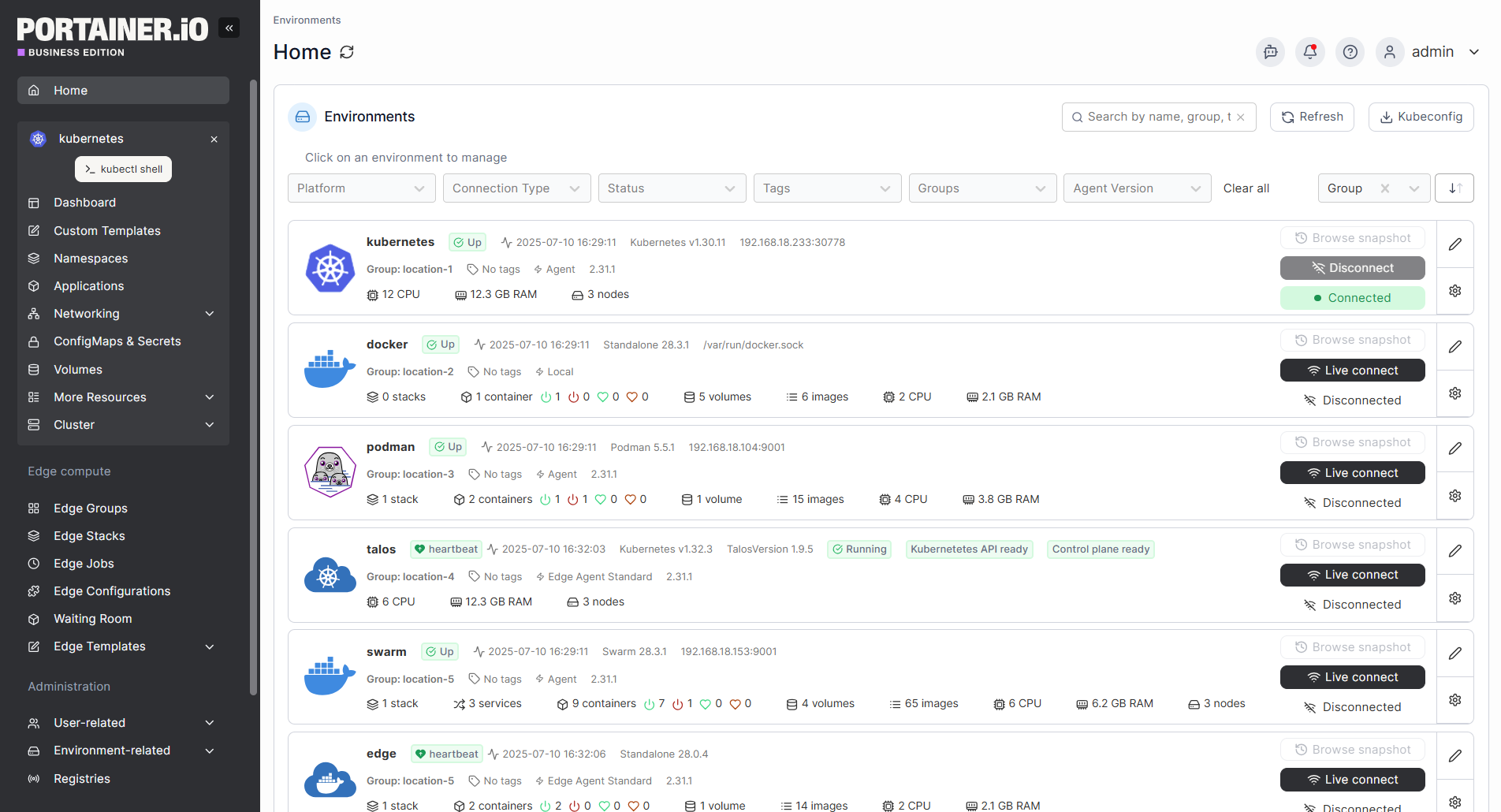
Portainer is your all-in-one container management platform for managing containerized environments, offering a wide range of functionality tailored to meet the needs of individual developers and enterprise teams alike. We often hear from our users, “Wow, I didn’t know Portainer could do that!” So here’s a list of what you can do with Portainer.
Edge / IIoT specific features
Frequently asked questions
A “node” can be described as a “server” (whether this is an actual physical server, a VM, a Raspberry Pi, your desktop or laptop, an industrial computer, or an embedded computing device) that is capable of running containers (via Docker, Kubernetes or another orchestrator) which is either running the Portainer Server or is under the management of a Portainer Server installation.
View “What’s a Node for licensing purposes?” for more information.
We also offer a range of pricing for different node sizes:
- For Edge Compute nodes; Edge Server (<= 16 cores), Edge Gateway/ Industrial/PC (<= 10 cores), Edge Linux PLC/ Mini PC (<= 4 cores) or IoT Sensor nodes (<=1Ghz).
No. A single Portainer license supports container management across all orchestrators and environments.
Portainer Community Edition is our free and open source version, most suited to individuals or small self-managing teams. It is community supported. CE is perfect for home lab use and learning how to manage containers.
Portainer Business Edition is our premium offering that includes features for Security, Access Management and Permission, and Auditing, making it more suitable for organizations.
For more information visit: Portainer Community Edition vs Portainer Business Edition, What's the Difference?
Upgrading from Community Edition to Business Edition is as simple as deploying the Portainer Business instance instead of Community Edition, reusing all of your existing database/settings.
Downgrading from Business Edition to Community Edition can be tricky. Please visit Can I downgrade from Portainer BE to Portainer CE on our Knowledge Base to ensure you follow the correct process.
Get started with Portainer today
Book an Enterprise demo to explore how we simplify container management at scale.