Your industrial edge devices are rarely compromised by sophisticated attackers. You lose control through outdated software, containers drifting from approved configurations, and a fleet too large to manage manually.
Knowing exactly what runs on every edge device, controlling who can change it, and fixing vulnerabilities before they become incidents is what Industrial IoT security actually requires.
This guide covers the operational controls, security checklist, and tools that make all three possible at scale.
Why Industrial IoT Security Is Harder Than Traditional IT Security
When a corporate laptop gets compromised, you lose data. When an IIoT edge device is compromised, you lose production. In the worst cases, people get hurt.
The scale of exposure is growing fast. Connected IoT devices were projected to reach 21.1 billion by the end of 2025; manufacturing has been the most attacked industry globally for four consecutive years; and unscheduled downtime already costs the world's 500 largest companies $1.4 trillion annually.
What makes IIoT security difficult isn’t the threat actors. It’s the structural constraints that make standard IT security practices impossible to apply:
- No patch windows. Most OT systems run 24/7. Downtime for updates isn’t scheduled; it’s an emergency.
- Decade-long device lifespans. IIoT hardware deployed in 2010 wasn’t designed with modern threats in mind, and replacing it mid-operation isn’t realistic.
- Proprietary protocols. Modbus, DNP3, and PROFINET don’t speak the same language as standard IT monitoring tools, creating blind spots across the OT network.
- Unpatched vulnerabilities everywhere. In the first half of 2023 alone, 227 of the 670 ICS vulnerabilities reported to CISA lacked available fixes. Yet those devices stayed in production.
- Physical consequences. A misconfigured firewall rule in IT causes a help desk ticket. The same mistake in OT can trip a safety system or halt an entire production line.
Tweaking your existing IT security approach won't cut it here. The differences run deeper, and nothing shows that more clearly than comparing IIoT directly against consumer IoT.
Key Differences Between IIoT and IoT Security
IIoT and consumer IoT share the same networking concepts, but the environments, stakes, and constraints are completely different.
Here are the major differences between these two security models:
{{article-cta}}
Building a Secure Operational Model for Industrial IoT
Firewalls protect network perimeters. They don’t tell you what software version is running on device 347 in Facility B, or whether it drifted from its approved configuration three weeks ago.
This framework covers four operational controls that actually reduce IIoT risk at scale.

Centralized Visibility Across Distributed Devices
By the time you discover 40 devices running a vulnerable image, the exposure has lasted weeks. That’s what reactive security looks like at scale, and it’s the default state for any team without centralized visibility.
Centralized visibility gives you the ability to answer the questions that matter for security, in real time:
- Workload inventory: See every container running on every edge device from a single interface, along with its image name, version, and current status
- Version tracking: Identify which devices run the approved image versus outdated versions instantly, across your entire fleet
- Configuration drift detection: Flag when a device’s running state differs from its intended configuration. This is usually the first sign that something has changed without authorization
- Full audit trail: Log every workload change across every device, giving your security and compliance teams the record they need for incident investigation and regulatory reporting
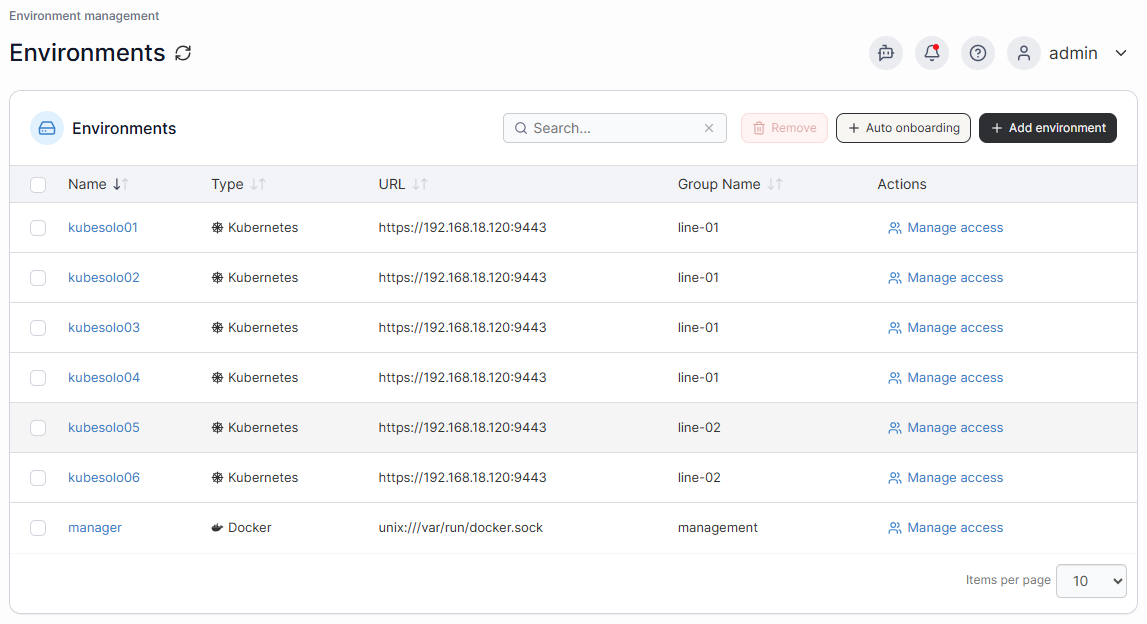
Portainer’s IoT device management dashboard provides this fleet-wide view across all managed edge environments, whether you’re managing 50 or 5,000 devices.
Book a demo to see how Portainer monitors containers’ performance, resource usage, and application health in real time.
Logical Grouping of Devices
Not every edge device carries the same risk. A device translating industrial protocols on the production floor and a device running analytics on the corporate IT network should never share a deployment boundary. One breach shouldn’t reach both.
Logical grouping allows you to enforce that distinction at the deployment level. Group devices by:
- Physical location: Facility A, Facility B, remote field sites
- Network zone: OT network, IT network, DMZ segments
- Function: Protocol translators, ML inference nodes, data collection devices
- Risk profile: Safety-critical processes versus non-critical monitoring workloads
Each group becomes an independent deployment target. A misconfigured update can’t reach production-floor devices unless it’s explicitly targeted at that group. A security policy applied to a zone takes effect across all devices in that zone simultaneously, without affecting devices in other zones.
Portainer’s Edge Groups make this concrete. You define the grouping criteria, assign devices, and every stack deployment respects those boundaries automatically.

Controlled, Staged Software Rollouts
The riskiest moment in IIoT security isn’t the vulnerability; It’s the patch. Pushing an update to every device in a facility simultaneously can turn a 5-minute fix into a 12-hour outage if something goes wrong.
Staged rollouts break the process into controlled phases with a validation gate between each one:
- Deploy to a small pilot group (5-10% of devices)
- Monitor for unexpected behavior, container restarts, or errors
- Expand to a larger validation group (25-50%) if the pilot passes cleanly
- Complete full fleet deployment only after the validation group confirms stability
If any phase shows problems, the rollout halts. Only a fraction of devices are affected, and reverting takes minutes rather than hours.
Modern container management platforms like Portainer provide this through Edge Stacks update configurations. Staged rollout is built directly into the platform. It requires no custom pipeline, scripting, or separate tooling to maintain.

Remote Update & Rollback Capabilities
A physical visit to update a remote edge device costs between $500 and $1,500 when you factor in technician time, travel, and production disruption. Across 500 devices at multiple sites, patching becomes financially impractical. That’s why many teams avoid it.
Unfortunately, it results in devices running outdated software for months because the cost of updating outweighs the perceived risk.
Remote update and rollback eliminate that tradeoff:
- Remote patching: Push security updates to all managed devices from a central interface, with no site visits needed and no production disruption from scheduling technicians
- Rollback on failure: Revert any device to its last known-good state in minutes, not days, if an update causes unexpected behavior
- Agent-level updates: Portainer’s Update & Rollback feature specifically manages the Edge Agent itself, the component that connects each device to the management platform, keeping the management layer current with the latest security fixes
- Closed vulnerability windows: Reducing the update cycle from weeks to hours means attackers have far less time to exploit a known weakness before it’s patched
The practical security gain isn’t just technical. When updating a device takes minutes instead of a scheduled site visit, you’ll actually do it. Regular patching is the single most effective way to control known vulnerabilities.
The operational controls in this framework focus on the software management layer. Before any container is deployed, the underlying environment needs to be hardened as well.
{{article-cta}}
A Practical Security Checklist for Industrial IoT Teams
Work through this checklist by category, assign ownership to each item, and treat anything unchecked as an open risk:
Network Segmentation
- OT and IT networks are separated by firewalls or DMZ
- IIoT edge devices sit in clearly defined network zones
- Traffic flows between zones are explicitly permitted; everything else is denied
- Remote access routes through a dedicated jump server or VPN, not direct connections
- OT protocols (Modbus, DNP3, PROFINET) are blocked from reaching IT networks directly
Device Hardening
- Default credentials changed on every device before deployment
- Unnecessary services, ports, and protocols disabled
- Secure boot enabled where hardware supports it
- Local firewall rules configured on each edge device
- Physical access to edge devices is restricted and logged
Software and Container Security
- All container images scanned for vulnerabilities before deployment
- Images pulled only from approved, trusted registries
- No unverified or public images running on production edge devices
- Every edge device runs the approved, current software version — verified centrally
- Update and rollback processes tested before a security incident requires them
Access Control
- Role-based access control enforced — operators, engineers, and admins have separate permissions
- Multi-factor authentication required for all management platform access
- Privileged access reviewed and revoked when roles change
- All configuration changes logged with user attribution
- Third-party vendor access time-limited and monitored
Patch and Vulnerability Management
- Asset inventory maintained, i.e., every edge device and software version documented
- Vulnerability scanning runs on a defined schedule
- Patch prioritization process exists for OT-specific CVEs
- Staged rollout used for all updates to avoid simultaneous fleet-wide failures
- Compensating controls in place for devices that can’t be patched
Monitoring and Incident Response
- Centralized logging collects events from all edge devices
- Alerts configured for unexpected container restarts, unauthorized images, or auth failures
- Incident response playbook documented for common IIoT breach scenarios
- Rollback procedure rehearsed, not just documented
- Post-incident review process defined
Lightweight Kubernetes at the Industrial Edge (Emerging Trend)
Docker is the dominant containerization runtime for IIoT today. Standard Kubernetes is too resource-heavy for most industrial edge hardware.
As edge hardware gets more capable, teams managing large IIoT fleets increasingly want orchestration consistency between cloud and edge environments, without separate tooling or retraining staff. The gap between what they want and what the hardware could support is closing fast.
That’s why the Portainer team built KubeSolo specifically to fill this gap. It’s a free, ultra-lightweight Kubernetes distribution designed for constrained IIoT hardware that standard distributions can’t run on. It integrates directly with Portainer, so your cloud and edge workloads live under the same management interface.
Get started to see how Kubesolo works in real-time.
Manage and Protect Distributed IIoT Devices at Scale with Portainer
Securing IIoT edge workloads gets harder as your fleet grows. Not because the threats change, but because manual processes don’t scale. At 10 devices, hand-managing updates works. At 200, it doesn’t.
Portainer provides centralized visibility and control over every containerized workload across your entire fleet. It works across both Docker and Kubernetes environments, so your team manages everything from a single interface without the enterprise overhead that makes other platforms impractical at the edge.
See how to gain full control of your edge fleet without adding operational overhead today.
FAQs
What is Industrial IoT Security?
It's the practice of protecting connected devices, edge infrastructure, and software workloads running across industrial environments like manufacturing and energy.
Is Docker or Kubernetes Better for IIoT Edge Devices?
Docker. Most IIoT hardware is not powerful enough for standard Kubernetes. KubeSolo is changing that for capable edge devices.
Can Portainer Manage Edge Devices Across Multiple Facilities?
Yes. Edge Groups organize devices by facility or network zone and are managed from a single interface without physical access.
What’s the Biggest IIoT Security Mistake Operations Teams Make?
Avoiding updates. Fear of downtime keeps vulnerable software running. Staged rollout and instant rollback make regular patching safe.
Does Portainer Replace a SCADA or OT Security Platform?
No. Portainer manages containerized software workloads on edge devices. OT platforms like Claroty monitor industrial protocols and network traffic.



.png)
.png)
.png)