Docker Swarm was never built for where container infrastructure is heading. It was built for simplicity, and for years, that was enough. But Docker Engine v29 introduced breaking changes that disrupted storage, networking, and security integrations that Swarm environments depend on daily.
If you're on Swarm and wondering what comes next, the answer is Kubernetes with K3s, Nomad, ECS, and Red Hat OpenShift serving specific use cases. If you’re starting a new container environment from scratch, start with Kubernetes.
This guide explains why, walks through the specific options for teams at different stages of readiness, and shows how Portainer helps you manage the transition without disrupting production.
Why It's Time to Look for Alternatives to Docker Swarm
Docker Swarm worked until it didn't. Here are reasons why you should consider a Docker Swarm alternative.
Docker Engine v29 Broke Things Swarm Users Depend On
In November 2025, Docker released Engine v29.0.0, calling it a foundational release. For Swarm operators, it was more disruptive than that.
Firstly, there was a clear caution at the beginning of the update documentation.
These breaking changes included:
- Minimum API version raised to v1.44: Any tooling or storage plugin built against older Docker APIs stopped working immediately.
- cgroup v1 deprecated: Docker v29 formally deprecated cgroup v1 support. While removal isn't until May 2029, any infrastructure still on older kernels needs a migration plan now, not later.
- nftables introduced as the new firewall backend: Swarm's overlay networking and routing mesh depend on specific iptables behaviors. The shift to nftables broke existing firewall rules, caused connectivity failures between containers on overlay networks, and blocked traffic on published ports.
- Overlay networking overhauled: The DOCKER-ISOLATION-STAGE-1 and DOCKER-ISOLATION-STAGE-2 chains were removed entirely. Teams running mixed-version Swarm clusters hit networking failures that require manual remediation.
None of these are minor edge cases. They affect storage, networking, and security, the three pillars that Swarm environments depend on daily.
The Ecosystem Behind Swarm Is Shrinking
Swarm itself still runs, but everything built around it is being discontinued, deprioritized, or redirected toward Kubernetes.
Mirantis, which acquired Docker's enterprise business in 2019 along with the Docker Swarm IP, released Mirantis Kubernetes Engine (MKE) 4 with a complete focus on Kubernetes. Swarm support is limited to MKE 3, and no new features are planned for it.
As Mirantis CEO, Adrian Ionel stated at the time of the acquisition, "We're buying Docker Enterprise for a couple of reasons. One is to accelerate our journey towards providing Kubernetes as a Service to the world for multicloud and hybrid use cases."
The container orchestration industry followed the same path. According to the 2025 CNCF Annual Cloud Native Survey, 82% of container users now run Kubernetes in production, up from 66% in 2023. Observability tools, CI/CD platforms, service meshes, and cloud providers have all built their integrations around Kubernetes.
Do you want to migrate to Kubernetes without disrupting your live workloads? Book a Portainer demo to see how to manage Swarm and Kubernetes side by side, migrate your workloads incrementally without causing downtime, and build operational confidence on Kubernetes before cutting over completely.
Swarm Has No Answers for Modern Operational Requirements
Enterprise teams running production workloads today need granular role-based access control (RBAC), multi-cluster visibility, policy-driven deployments, and deep integration with GitOps pipelines. Swarm provides none of those natively.
A Redditor explicitly mentioned that Docker Swarm's basic features can't handle complex container orchestration tasks.
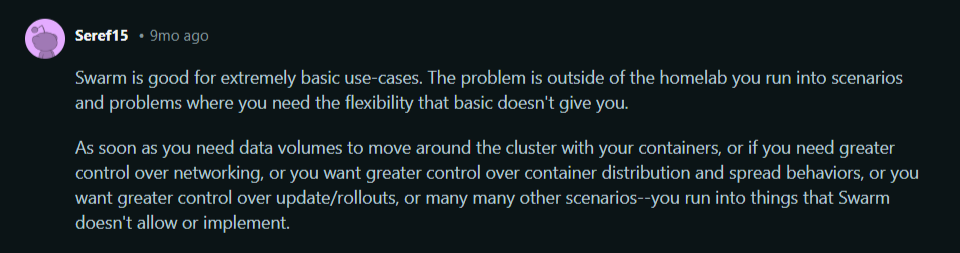
Source: A Reddit thread on Docker Swarm's limitations
A G2 user also noted, “Compared to more robust orchestration platforms like Kubernetes, Docker Swarm has a more limited feature set. It may not offer the same level of advanced functionalities, customizability, or ecosystem integrations as some other container orchestration tools.”
Docker Swarm's access control model is basic, its observability is limited, and extending it requires workarounds that add complexity without adding capability.
Key Considerations If You Are Migrating From Docker Swarm
Before picking a platform, these are the factors that actually determine whether the migration succeeds:
Take a Full Inventory of What You're Actually Running
Most teams underestimate what's in their Swarm environment until they try to move it.
Start by cataloging every service, volume, network, secret, and config currently deployed. Identify which workloads are stateless (easier to migrate) and which are stateful (require dedicated planning).
Also, include every third-party integration, storage plugin, and published port.
Portainer's centralized dashboard makes this audit faster. It gives a single view of all your running stacks, services, volumes, and networks across your Swarm environment, so nothing gets missed before the migration begins.
Book a demo to see how Portainer works.
Match the Alternative Platform to Your Team's Skill Level
Not every team is ready for Kubernetes, and forcing a complex platform on an unprepared team creates more problems than it solves.
If your team is small, already stretched, and comfortable with Docker-native workflows, a simpler alternative or a managed container platform may be the right intermediate step. If your team has DevOps capacity and the workloads justify it, Kubernetes is the stronger long-term investment.
Plan for a Parallel Running Period, Not a Hard Cutover
Shutting down Swarm and switching platforms in a single event is a high-risk approach. A parallel running period is safer.
Run your target platform alongside Swarm, migrate workloads incrementally, validate each service in the new environment, then decommission from Swarm only when confidence is high. This approach keeps production stable, gives the team real experience on the new platform before it's load-bearing, and makes rollback straightforward if something breaks.
Best Docker Swarm Alternatives at a Glance
Kubernetes: Best for Teams Ready to Scale Beyond Swarm's Limits

Kubernetes is the most widely adopted container orchestration platform in the world, and the right destination for virtually every team migrating from Docker Swarm. If you’re starting a new container environment today, there is no longer a strong reason to start anywhere else.
It handles everything Swarm does, plus advanced scheduling, multi-cluster operations, granular RBAC, and a vast ecosystem of integrations.
The only limitation is the platform's complexity. Raw Kubernetes assumes strong CLI expertise and deep platform knowledge. Teams moving from Swarm's simplicity will feel that gap immediately, which is why pairing Kubernetes with a management platform like Portainer is how most teams bridge the transition without stalling on the learning curve.
Key Features
These three features are the most significant upgrades for teams migrating from Swarm.
Advanced Workload Scheduling and Auto-Scaling
The Horizontal Pod Autoscaler (HPA) scales workloads up or down based on CPU usage, memory pressure, or custom metrics. The Cluster Autoscaler adds or removes nodes based on demand. Vertical Pod Autoscaling adjusts resource requests automatically over time based on observed usage.
Native RBAC and Namespace-Based Multi-Tenancy
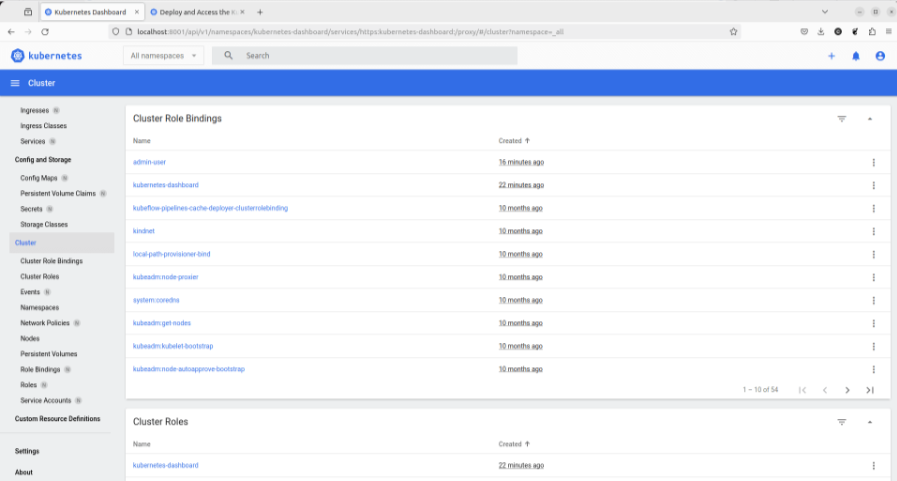
Swarm offers no native access control beyond Docker daemon access. Anyone who can reach the daemon can do anything. Kubernetes replaces that with a full role-based access control system built into the platform.
Namespaces provide logical separation between teams, environments, or applications within a single cluster. Roles and ClusterRoles define exactly what actions a user or service account can perform. RoleBindings assign those roles at the namespace level, while ClusterRoleBindings apply them cluster-wide.
If you manage this through a UI rather than raw manifests, Portainer's RBAC layer maps these Kubernetes primitives into team-based permission management without requiring deep expertise to configure or maintain.
Rich Ecosystem and Native Cloud Provider Integration
Observability tools like Prometheus and Grafana connect natively through Kubernetes metrics APIs.
CI/CD platforms, including ArgoCD, FluxCD, and GitHub Actions, have purpose-built Kubernetes integrations for automated deployments. Service meshes like Istio and Linkerd add mTLS, traffic shaping, and fine-grained observability between services.
Also, every major cloud provider offers a managed Kubernetes service with native integrations.
Pricing
Kubernetes is open-source and free.
Where Kubernetes Shines
- Production-grade scalability: Kubernetes handles workload scaling, self-healing, and rolling deployments automatically. Applications stay available through traffic spikes, node failures, and deployments without manual intervention.
Image: Kubernetes G2 review on workload scaling
- Ecosystem depth: Every major observability, CI/CD, security, and networking tool has a Kubernetes integration.
- Long-term investment: The platform has the broadest community, the most active development, and the strongest vendor support of any orchestrator available.
Where Kubernetes Falls Short
- Steep learning curve: Kubernetes introduces concepts that Swarm doesn't have: pods, namespaces, ingress controllers, persistent volume claims, and more. Teams without DevOps experience might have difficulty operating it confidently in production.
Image: Kubernetes G2 review on its steep learning curve
Pro tip: Portainer offers a Kubernetes Managed Service where the Portainer team sets up and manages your container infrastructure for you, fully maintained and supported.
Contact our Managed Services team to see how Portainer's engineers reduce Kubernetes management workloads for teams.
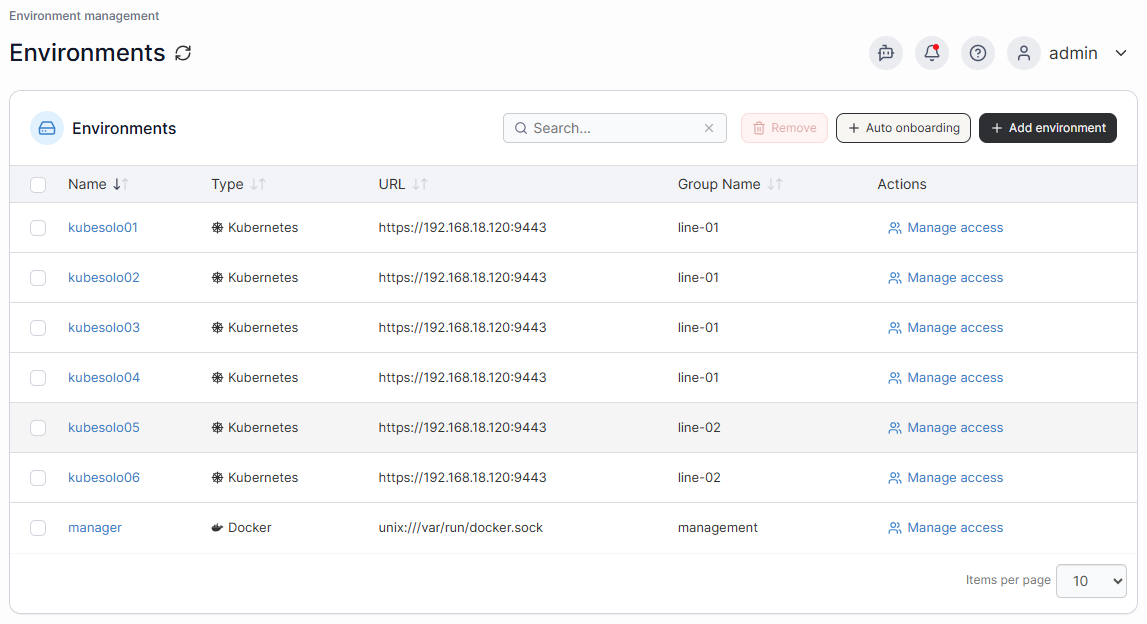
- No unified view across multiple clusters and environments: Kubernetes gives you powerful tooling within a single cluster, but managing multiple clusters across on-prem, cloud, and edge environments requires stitching together separate dashboards, CLI contexts, and access control systems.
Pro tip: Portainer's multi-environment management connects every Kubernetes cluster, regardless of where it runs, into a single interface with consistent access control and visibility across all clusters.
Customer Reviews
"What I like most about Kubernetes is how powerful it is for managing containerized applications at scale. It automates deployment, scaling, and load balancing, which takes a lot of manual work off the team. Once everything is set up, it's very reliable and makes it easier to keep applications running smoothly even as demand changes." G2 reviewer.
"The biggest challenge with Kubernetes for me is the steep learning curve. It introduces many concepts—such as pods, services, ingress, namespaces, and controllers—which can feel overwhelming, especially for newcomers or smaller teams without dedicated DevOps experience." Shiv B.
Who Kubernetes Is Best For
- Teams with DevOps or platform engineering capacity: Organizations that have, or are building, dedicated infrastructure expertise will get the most value from.
- Production SaaS and distributed applications: Workloads that need autoscaling, rolling deployments, multi-tenancy, and high availability are exactly what Kubernetes was designed for.
Further reading: Docker Swarm vs Kubernetes
K3s: Best for Lightweight Kubernetes at the Edge
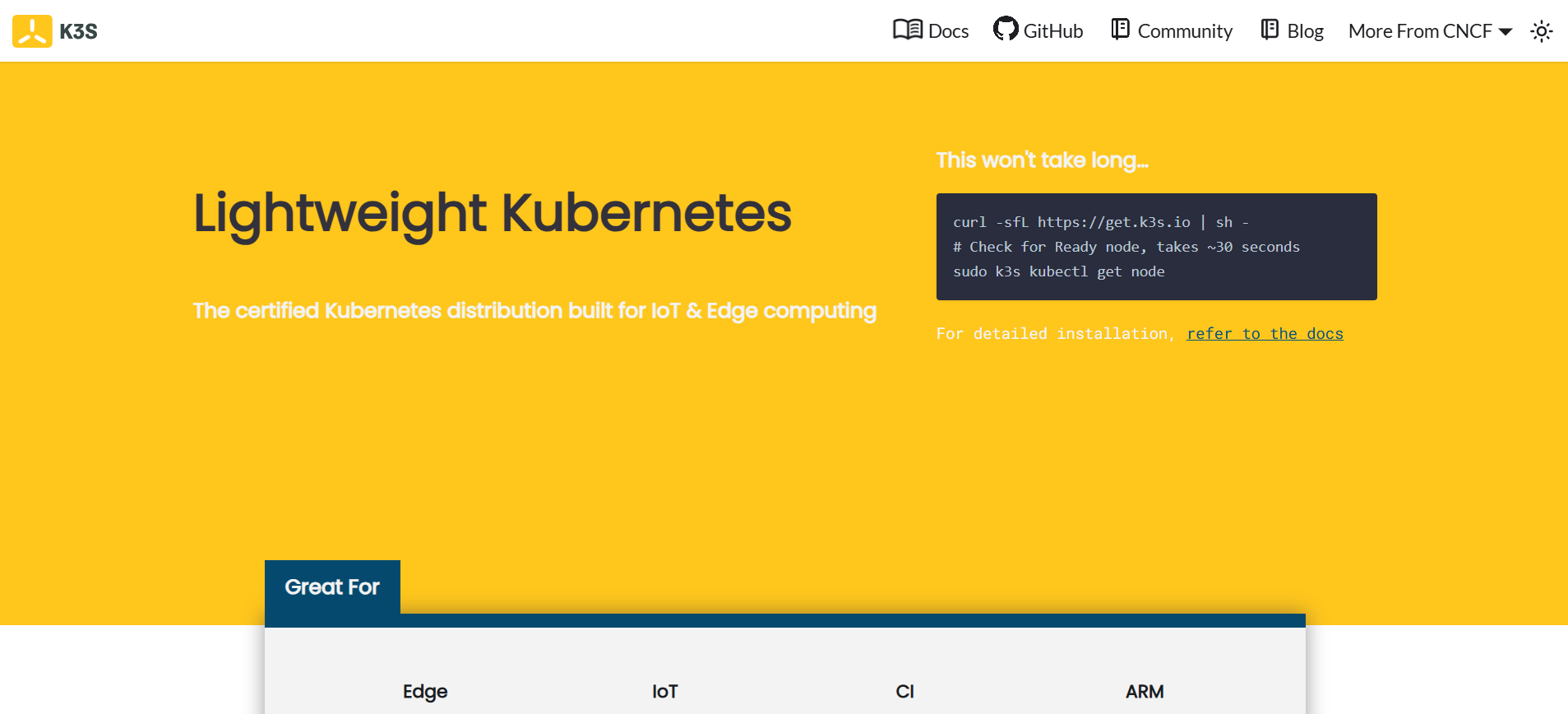
K3s is a fully certified Kubernetes distribution built for resource-constrained environments. It packages the full Kubernetes API into a single binary under 100MB, stripping out legacy and cloud-provider-specific components that most edge and IoT deployments don't need.
For Swarm users running on modest hardware or remote infrastructure, K3s offers a genuine path to Kubernetes without the full operational weight. It's the right choice when you need Kubernetes compatibility but standard distributions are too resource-heavy for your hardware.
Key Features
- Single binary installation: The entire K3s distribution ships as a single binary, making deployment and upgrades significantly simpler than with standard Kubernetes.
- Built-in containerd runtime: No separate container runtime installation required. K3s ships with containers pre-configured and ready to run.
- SQLite as default datastore: Replaces etcd with SQLite for single-node deployments, reducing memory requirements and operational complexity on smaller hardware.
- Embedded load balancer and ingress: Ships with Traefik as the default ingress controller and ServiceLB for load balancing, eliminating the need to configure these separately.
Pricing
K3s is open-source and free.
Where K3s Shines
- Edge and IoT deployments: K3S runs on hardware as small as a Raspberry Pi with as little as 512 MB of RAM. If you manage your containers on remote or resource-constrained devices, it delivers full Kubernetes capability where standard distributions simply won't fit.
Source: Reddit
- Easy to set up: K3s installs with a single command and requires minimal configuration to get a working cluster.
Where K3s Falls Short
- Not ideal for large-scale production clusters: K3s trades some of Kubernetes's production-grade capabilities for simplicity. SQLite, for example, as the default datastore, doesn't support high-availability multi-node clusters without switching to an external datastore such as etcd or PostgreSQL.
- Smaller ecosystem than standard Kubernetes: While K3s runs standard Kubernetes workloads, some enterprise tooling and cloud provider integrations are tested and documented primarily for standard distributions.
Customer Reviews
"K3S is pretty easy to setup. It's also not very difficult to bootstrap it via Ansible. The challenge is mostly with configuration." Redditor
"k3s beautiful little piece of software, works so well, dead simple UX" Dasbitshifter
Who K3s Is Best For
- Edge and IoT teams: Organizations running containers on remote, resource-constrained, or industrial hardware where a full Kubernetes distribution is too heavy.
- Small teams wanting Kubernetes without the complexity: Teams migrating from Swarm who want standard Kubernetes compatibility on modest infrastructure without the full operational overhead of a production-grade distribution.
{{article-cta}}
HashiCorp Nomad: Best for Teams Not Ready for Kubernetes Complexity
Nomad is a flexible workload orchestrator from HashiCorp that handles containers, binaries, Java applications, and virtual machines from a single scheduler.
For teams running mixed containerized and non-containerized workloads who aren't yet ready for Kubernetes's operational weight, Nomad is a viable stepping stone. But it's worth noting that the ecosystem has converged firmly on Kubernetes, and the long-term path for most teams still leads there.
Key Features
- Multi-workload scheduling: Orchestrates containers, raw binaries, Java JARs, and virtual machines from a single unified scheduler, unlike Kubernetes, which is containers-only.
- Single binary architecture: Nomad's entire client and server stack ships as a single binary, making installation and upgrades straightforward across any infrastructure.
- Native HashiCorp ecosystem integration: Works natively with Vault for secrets management, Consul for service discovery, and Terraform for infrastructure provisioning out of the box.
- Lightweight resource footprint: Nomad's control plane consumes significantly fewer resources than Kubernetes, making it viable on smaller infrastructure without dedicated control-plane nodes.
Pricing
Where Nomad Shines
- Mixed workload environments: Teams running a combination of containerized and non-containerized applications get genuine value from Nomad's unified scheduler.
- HashiCorp-heavy infrastructure: Organizations already using Vault, Consul, and Terraform get a significant integration advantage with Nomad. Secrets injection, service discovery, and infrastructure provisioning connect natively without custom configuration or third-party plugins.
Image: Reddit review on Nomad pros
- Simpler operational model than Kubernetes: Nomad has far fewer concepts to learn than Kubernetes. There are no pods, no controllers, no ingress objects.
Where Nomad Falls Short
- Licensing concerns following the BSL switch: In 2023, HashiCorp moved Nomad from the Mozilla Public License to the Business Source License (BSL). The BSL restricts the use of Nomad in competing commercial products without a separate agreement.
Image: Reddit review on Nomad pricing issue
- No built-in container image management or registry integration: Nomad relies on external tooling for image management, vulnerability scanning, and registry access control.
Customer Review
A Redditor shared, "I was looking at Nomad for its simplicity, but its licensing model does not make me 100% confident about its future. Besides, it does not seem to gain traction these days."
Who Nomad Is Best For
- Teams running mixed containerized and non-containerized workloads: Organizations that can't yet move everything into containers but need unified orchestration across all workload types.
- HashiCorp ecosystem users: Teams already running Vault, Consul, and Terraform who want a natural orchestration fit without adopting an entirely new tooling stack.
Amazon ECS: Best for Teams Already Deep in the AWS Ecosystem
Amazon Elastic Container Service (ECS) is AWS's native container orchestration platform. It removes cluster management overhead entirely by handling the control plane for you, leaving you to focus on deploying and running workloads.
For Swarm users already operating on AWS infrastructure, ECS offers a low-friction migration path with deep native integrations across IAM, ALB, CloudWatch, and Fargate serverless compute.
The trade-off is lock-in: ECS is an AWS-only platform with no meaningful portability outside AWS.
Key Features
- Fargate serverless compute: Run containers without managing EC2 instances. AWS provisions and scales the underlying compute automatically based on workload requirements.
- Native AWS service integration: ECS connects directly to IAM for access control, ALB for load balancing, CloudWatch for logging and monitoring, and ECR for container image management.
- Task definition model: Workloads are defined as tasks that group one or more containers, along with their resource requirements, networking, and storage configurations into a single declarative unit.
- Deep security integration: IAM roles can be assigned at the task level, giving individual containers fine-grained AWS permissions without exposing broad credentials to the entire cluster.
Where ECS Falls Short
- Hard AWS lock-in: ECS workloads are not portable. Task definitions, networking configurations, and service integrations are all AWS-specific.
- No multi-cloud or hybrid visibility: Teams running workloads outside AWS lack a unified view across environments. ECS only sees what's within AWS, creating blind spots for organizations with mixed infrastructure.
Pro tip: Portainer provides unified visibility and management across cloud, on-prem, and edge environments from a single interface. If you have workloads split across AWS and other environments, Portainer provides consistent governance and access control without needing separate tooling for each platform.
- Limited Kubernetes compatibility: ECS uses its own task and service model rather than Kubernetes-native constructs. If you eventually want to move to Kubernetes, whether EKS or otherwise, there might be significant rework to your workload definitions and tooling, since nothing transfers directly.
Red Hat OpenShift: Best for Enterprises With Strict Compliance Requirements
Red Hat OpenShift is an enterprise Kubernetes platform with hardened security defaults, built-in developer tooling, and vendor-backed support. It sits atop standard Kubernetes and adds opinionated security policies, an integrated CI/CD pipeline, a developer console, and out-of-the-box alignment with the CIS benchmark.
OpenShift is built for enterprises where security and compliance are non-negotiable.
Key Features
- Hardened security by default: OpenShift enforces Security Context Constraints (SCCs) out of the box, restricting what containers can do at the kernel level without requiring manual policy configuration.
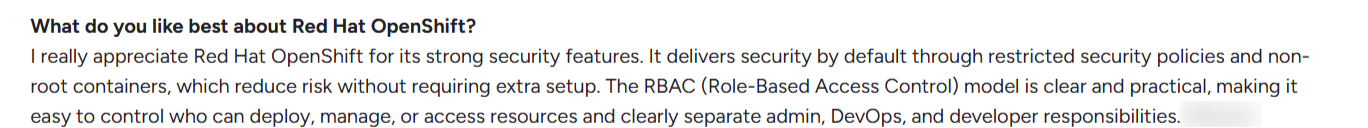
Image: OpenShift G2 review on its strong security features
- Built-in CI/CD pipelines: OpenShift Pipelines, based on Tekton, provides a native Kubernetes CI/CD system without requiring a separate Jenkins or GitHub Actions setup.
- Developer self-service console: A web-based console lets developers deploy applications, view logs, and manage resources without needing CLI access or Kubernetes expertise.
- Multi-cluster management via ACM: Advanced Cluster Management (ACM) provides centralized governance, policy enforcement, and visibility across multiple OpenShift clusters from a single control plane.
Where OpenShift Falls Short
- Significant cost barrier: For small and mid-sized teams, the cost is difficult to justify compared with fully open-source Kubernetes distributions that offer comparable functionality with greater flexibility.
- Weak built-in monitoring dashboards: OpenShift's built-in viewing dashboards are limited despite its enterprise price point. Visualizing workload health and metrics at the depth most teams expect requires configuring Grafana separately, adding unnecessary setup overhead on a platform of this scale.
Dinesh M. mentions, “I find that the monitoring features in Red Hat OpenShift could be improved. Specifically, there is a lack of inbuilt viewing dashboards that I believe would enhance the usability and effectiveness of the monitoring capabilities.”
Further reading: Best 5 OpenShift Alternatives
Portainer: Your Operational Control Plane for Multi-Cluster Environments
Portainer is not a Docker Swarm alternative but the management layer that makes migrating away from Swarm operationally sustainable.
Every alternative in this list solves a different problem. Kubernetes gives you scale and ecosystem depth. K3s gives you Kubernetes without the weight. Nomad gives you flexibility across workload types. But none of them solves the operational layer, which is visibility, access control, and day-to-day governance across environments
Portainer sits above your orchestrators as a unified management interface. It connects Swarm and Kubernetes environments side by side, giving your team a single pane of glass for workload management, RBAC, and operational governance, so you can run both in parallel, migrate incrementally, and decommission Swarm only when you're confident your Kubernetes environment is production-ready.
For instance, Ilionx replaced Rancher with Portainer to manage their Kubernetes platforms, avoiding the need to hire two additional engineers. They increased uptime by over 90%.

If you're ready to migrate from Swarm and want a practical plan tailored to your specific environment, request a Swarm Platform Assessment to get a migration roadmap for your workloads, timeline, and team.
FAQs on Docker Swarm Alternatives
- Is Docker Swarm still supported in 2026?
Yes, but in a limited capacity. Docker Swarm still runs production workloads, but active development has effectively stopped.
- Can I run Docker Compose files on Kubernetes after migrating from Swarm?
Yes, with conversion. Tools like Kompose translate Docker Compose files into Kubernetes manifests, giving you a starting point for migration. However, the output rarely maps cleanly to production-ready Kubernetes configurations. Treat converted manifests as a first draft, not a finished result.
- What is the best alternative to switch to from Docker Swarm?
Kubernetes. It is the industry standard for container orchestration. It offers the broadest ecosystem support, the strongest long-term investment, and the deepest integrations across cloud providers, observability tools, and CI/CD platforms.





